Key Takeaway
Several recent data breach incidents involved misconfigured MongoDB databases. MongoDB is a popular open source document database for big data and often used for storing sensitive data including Personally identifiable information (PII) and Protected Health information (PHI) data. Off late, Data breach has become a business reality. It is no longer a question of if but when. As businesses leverage the power of big data, cloud, and internet of things to deliver new services and products, they need to take appropriate steps to manage and mitigate the data breach risks.
Mongo DB Data Breaches
MongoDB’s open source version runs with the default TCP port 27012.Security researchers1 found many MongoDB servers running in publicly accessible space on the internet. In the absence of appropriate security protocol, this often resulted in data breaches. Following list highlights some of the recent data breach incidents involving Mongo DB.
- Oct,2016 – Hacker stole 58 million customer information from MongoDB database of Modern Business Solution2– A Texas-based data management solution provider.
- Jun,2016 – Hacker leaked 36 million+ Mongo DB accounts3
- Apr, 2016 – AWS hosted MongoDB configured incorrectly – No password was required to access this database – resulting in data exposure of 93 million Mexican voters4.
- Dec, 2015 – A MongoDB database exposed personal information of over 191 million US voters5
Key Challenges
With the rapid adoption of the document based big data repositories across industries, the amount of sensitive data that is stored, processed and used by MongoDB-based applications on-premise and in the cloud, has exploded.
While a large percentage (40%) of data breaches are results of hacking or malicious attack and often a popular topic of discussion in social media, employee and vendor error along with system glitches are the primary reasons for the majority of the data breaches6,7,8 .
In addition to setting up correct security configuration for protecting data housed in MongoDB, organizations need to establish an appropriate level of encryption to protect sensitive information such as PII and PHI data to prevent employee and third party related exposures. Only Four percent (4%) of the 5.3 Billion records exposed since 2013 due to data breaches was encrypted9 and hence did not result in any negative impact.
With so much data being stored in the MongoDB and exchanged between on-premise systems, mobile systems, and cloud-based applications, it is nearly impossible to identify and control sensitive information without a comprehensive approach.
Best Practices for Managing MongoDB data breach risks
- Establish and Monitor Security Set-up: MongoDB comes with a number of robust security An automated and ongoing audit is recommended to determine if the applied security set-up aligned with the design specification.
- Look for Internet Exposure: If MongoDB is deployed in the cloud, activate MongoDB’s cloud manager feature to monitor if any of the hosts is exposed to public internet
- Establish application level encryption: Application level encryption provides encryption on a per-field or per-document basis within the application layer. There are several commercial encryption technologies that can be used. We do not recommend drive encryption since it logs and exports may contain plain text data which may result in data exposure.
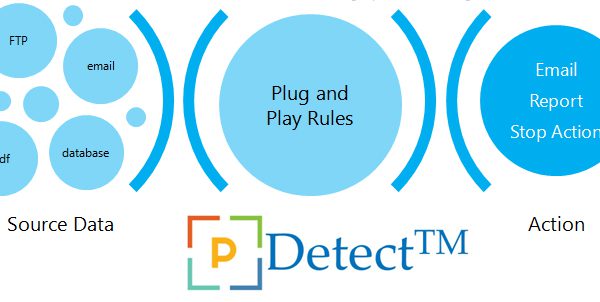
- Monitor MongoDB to detect sensitive information: Continuously look for the presence of sensitive information within the MongoDB and the corresponding log and export dumps using automated tools.
Bottom-line
Just because you have established security and encryption policies, do not assume your developers and users are adhering to the established policy. With the advent of rapid release cycle of applications and resource turnover, monitoring the security policy and encryption is an imperative for managing data breach risk.
- http://www.theregister.co.uk/2016/05/03/mongodb_security_breaches_vp_speaks/
- https://www.hackread.com/unsecured-mongodb-database-58m-accounts-leaked/
- https://www.hackread.com/hacker-leaks-36-million-mongodb-accounts/
- http://www.chicagocomputernetwork.com/2016/04/25/no-password-database-error-exposes-info-on-93-million-mexican-voters/
- http://www.theregister.co.uk/2015/12/28/security_researcher_spots_191_millionrecord_us_voter_database_online/
- 2016 Cost of Data Breach Study: The United States, Ponemon Institute LLC June 2016 – sponsored by IBM
- http://www.idtheftcenter.org/images/breach/ITRCBreachStatsReportSummary2015.pdf
- https://www.egress.com/en-US/blog/human-error-main-cause-of-data-breaches
- http://breachlevelindex.com/